Pentest: Realistic Tests for Real Vulnerabilities
A pentest simulates the approach of real attackers to identify security gaps early - before they can be exploited. Unlike automated scans, the focus is on manual analysis, realistic attack paths, and actual impact.
The goal is not a long list of theoretical vulnerabilities, but solid insights into what is actually exploitable - and how these risks can be effectively remediated.
What Are You Really Protecting?
Many organizations have only a few truly critical assets that keep decision-makers up at night - things that must never be stolen, published, or damaged.
Typically these are:
- Money - Bank access, payment systems
- Customer data - Personal information, contracts, business relationships
- Business-critical systems - Production, control systems, infrastructure that cannot fail
- Trade secrets - Developments, strategies, formulas
These assets are threatened by different risks - depending on whether an attack comes from outside or inside.
External vs. Internal: Where Does the Attack Come From?

External Threats: Attacks from the Internet
External attackers try to penetrate the organization through publicly accessible systems.
Vulnerabilities in Public Systems
Outdated software, unpatched security flaws, or misconfigurations in websites, VPN gateways, or cloud services
Compromised Credentials
Weak passwords, missing multi-factor authentication, or credentials from previous data breaches
Social Engineering
Phishing via email, fake IT support calls, or targeted manipulation of employees

Internal Threats: When the Attacker Already Has Access
Internal attackers already have a foothold - whether through compromised employee accounts, malicious insiders, or successful external attacks.
Missing Network Segmentation
From a compromised workstation, all other systems, servers, and databases are directly accessible
Excessive Permissions
Normal user accounts have access to critical systems or can escalate their own privileges
Unsecured Internal Systems
Servers, databases, or industrial controls without authentication, with default passwords, or outdated software

Cross-Cutting Risks
Some threats work both from outside and inside:
Malware
Infostealers, ransomware, or remote access trojans that infiltrate from outside or spread from within
Custom-Developed Software
Security issues in internally developed applications that can be exploited both externally and internally
Supply Chain Risks
Compromised vendors, external access points, maintenance access, or integrated third-party systems
The Right Scope for Your Pentest
For this reason, based on our experience, it often doesn't pay off for many organizations to extend the scope of a pentest across the entire company.
The time investment for a pentest has virtually no fixed limits - tests can last a few days or several weeks. This adds up quickly and isn't always goal-oriented.
Much more important is to first understand your organization and define the right scope together.
Together we also decide how closely the test should mirror the approach of a real attacker.
Blackbox Pentest
Want to assess your risk as realistically as possible?
We receive no information and must discover everything ourselves. Ideal for the most realistic risk assessment.
Greybox Pentest
Are you more concerned about internal risk, such as employees with insider knowledge?
We receive comparable information to an average employee, e.g., normal credentials or VPN access.
Whitebox Pentest
Is your IT already well-secured and you want to ensure that even hidden vulnerabilities are found?
We have access to documentation and credentials to test in a targeted and efficient manner.
Not every pentest examines the same systems or the same depth. What matters is the scope: which parts of the IT landscape are tested.
With increasing test depth, the scope expands - from a targeted entry test to examining the entire organization. The following diagram shows these levels and puts them in context.
▲Pentest Focused on Initial Access
Scope: First access to the organization
Before attackers can target internal systems, exfiltrate data, or spread through the network, they need one thing above all: initial access.
In practice, this access rarely comes from highly complex technical attacks. Very often, humans are the decisive factor – despite firewalls, antivirus, and other technical security measures.
This pentest examines whether and how an attacker can gain access to your systems at all. Among other things, the following points are considered:
- Compromised credentials
- Missing or insufficient additional authentication measures
- Publicly accessible entry points
- First reachable internal systems and resources
The focus is not only on the entry itself, but also on what real risks arise immediately after a successful access.
Small scope | Low effort | Very high insight value
Our Pentests
Our pentests are characterized above all by high customization and very realistic attack simulation.
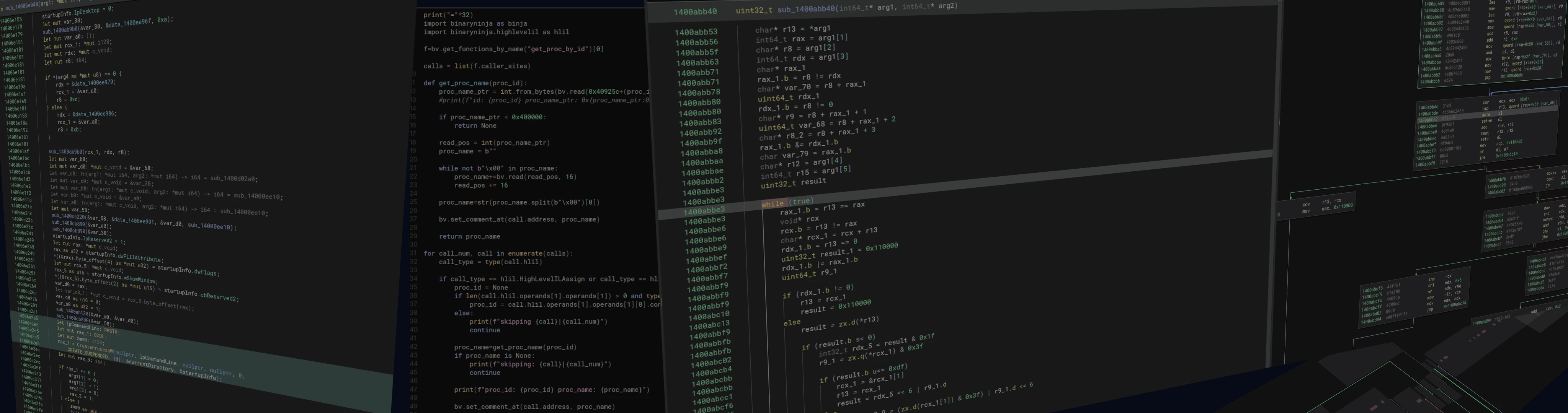
Analysis of Real Attacks
We examine real malware from current attacks to understand how organizations are actually compromised today - not just how attacks could theoretically unfold.
More Than the OWASP Top 10 Checklist
Standard works like the OWASP Top 10 are a sensible foundation, but alone they are not sufficient. Our tests go beyond simply working through lists and are oriented toward real attack scenarios.
Connected Attack Scenarios
We don't look at vulnerabilities in isolation, but show how individual weaknesses can be combined to compromise business-critical systems or data.
Individual Assessments Instead of Standard Templates
Every organization is different. That's why we tailor our tests specifically to your environment, rather than applying rigid testing programs uniformly to all clients.
Analysis of Custom-Developed Software
Custom applications and special solutions are often only superficially tested in standard tests. When needed, we analyze these specifically - down to detailed examination of program behavior or source code.
Clear Results with Business Focus
Our reports prioritize risks by their actual impact on your organization and deliver clear, understandable recommendations for informed decisions.
How a Pentest Works
A pentest is not a one-time scan, but a structured process with clearly defined phases and communication points. Transparency, traceability, and control are always the priority.
1Free Initial Consultation
Every pentest begins with a non-binding initial consultation.
In this conversation, we clarify together:
- which systems and assets are particularly critical for your organization
- which threat scenarios are realistic
- which type of test makes sense (e.g., initial access test, targeted system pentest, or comprehensive pentest)
The goal is a realistic assessment of whether and in what form a pentest makes sense for you.
2Scope & Kickoff Meeting
After deciding on a pentest, a joint kickoff meeting follows.
Here we define the binding framework of the test:
- Test scope and explicitly excluded systems
- Test type (blackbox, greybox, or whitebox)
- Test period and daily time windows
- Communication channels and emergency contacts
- Special conditions (e.g., production systems, maintenance windows)
This step ensures that the pentest is conducted in a controlled, safe manner without misunderstandings.
3Active Testing Phase (Penetration Testing)
During the agreed testing phase, we conduct attacks in a controlled and documented manner.
The following applies:
- Transparent communication: We inform you daily by email when we start and end testing.
- Clean approach: All activities are logged with timestamps, documented, and assigned to the agreed scope.
- Realistic attacks: Focus on manual testing, real attack paths, and actual impact - not on automated mass scans.
4Immediate Reporting of Critical Vulnerabilities
If critical, publicly accessible vulnerabilities are discovered during testing, we inform you immediately - even during the ongoing test phase.
This allows you to:
- initiate short-term countermeasures
- avoid potential damage
- prioritize risks without waiting for the final report
These reports are targeted, objective, and include the necessary technical details for quick response.
5Draft Report
After completing the testing phase, you first receive a draft report.
This contains:
- an executive summary
- identified attack chains and dependencies
- technical details and solid evidence
- prioritized and actionable recommendations
The draft serves to review content, clarify questions, and incorporate feedback on presentation.
6Final Report & Results Discussion
After the joint review, we create the final report.
In a closing meeting:
- we explain the results clearly
- put risks in realistic context
- answer open questions
- discuss sensible next steps
The final report is structured so that it is:
- understandable for management
- reproducible for IT teams
- reliable for auditors
7Retest & Verification
Later, we conduct a targeted retest.
We check:
- whether recommended measures have been implemented
- whether the previously identified vulnerabilities are still exploitable
The retest is deliberately limited to the originally affected systems and findings and enables a clear statement about whether the risks have actually been remediated.
Uncover Your IT Vulnerabilities - Let's Talk
Frequently Asked Questions
How long does a pentest take?
That depends on the scope:
- Initial access test (gaining first foothold only): 3 hours to a few days
- Specific system (targeted test of one application or service): 1-5 days
- Entire organization (all systems, multiple locations): 10-20+ days
In the free initial consultation, we can give you a concrete estimate for your situation.
Can the pentest damage our systems?
We work as carefully as possible and simulate attacks in a controlled manner.
Our safety measures:
- No destructive tests without explicit permission
- Recommendation for backups before critical tests
- Immediate notification of critical findings
- Emergency contact available at all times
- Daily updates on our activities
For production systems, we proceed with particular caution and coordinate every step in advance.
Who finds out about the results?
Only you. All findings are strictly confidential.
- NDA upon request
- Encrypted communication
- Secure data transfer
- Complete deletion after project completion
Do we even need a pentest?
Ask yourself the following questions:
- Do you have customer data that could be stolen?
- Would an IT outage paralyze your business?
- Do employees have access to critical systems?
- Are you reachable from the internet?
- Do employees use home office or VPN access?
- Would you know if someone unauthorized is currently in your network?
If you answered even one question with "yes": Yes, a pentest makes sense.
The average time to discover an attack is 277 days. During this time, attackers can cause enormous damage.
What's the difference between a pentest and a vulnerability scan?
Vulnerability scanner:
- Automated tools
- Fast and inexpensive
- Finds known vulnerabilities
- Many false positives
- No verification of actual exploitability
Pentest:
- Manual analysis by experts
- Time-consuming and thorough
- Finds unknown vulnerabilities and logic flaws too
- Verified, actually exploitable issues
- Realistic attack chains and real impact
Analogy: Scanners are like a metal detector on the beach - they beep at everything. Pentests are like an experienced burglar testing your house and telling you exactly where you're vulnerable.
What's the difference from red teaming?
Pentest:
- Focus: Find and document vulnerabilities
- You know testing is happening
- All findings are documented
- Timeframe: Days to weeks
- Goal: Uncover as many vulnerabilities as possible
Red Teaming:
- Focus: Achieve a specific goal (e.g., steal data, compromise a system)
- Only a few people know about it
- Also tests your detection and response capabilities
- Timeframe: Weeks to months
- Goal: Stay undetected and achieve defined objective
For most organizations, a pentest is the right starting point. Red teaming is suited for more mature organizations that want to test their blue team's defense capabilities.
Do we need to prepare anything?
For the pentest itself: No, nothing technical.
Helpful for planning:
- List of systems to be tested (rough overview is sufficient)
- Name contacts from IT and management
- Consider possible time windows
- Think about which systems are particularly critical
Depending on the test type (blackbox/greybox/whitebox), we need different amounts of information:
- Blackbox: Nothing at all - we find everything ourselves
- Greybox: Normal credentials like an employee
- Whitebox: Documentation, admin access, network diagrams
We clarify this together in the initial consultation.
How current are your attack techniques?
Very current.
We analyze new malware samples daily and extract from them:
- New evasion techniques for antivirus and EDR
- Current exploits and vulnerabilities
- Realistic attack chains from real criminals
- Functionality and tactics of current malware
These insights flow directly into our pentests. While other pentesters work with publicly known tools that every antivirus knows, we develop our own tools and adapt them to your environment.
The result: We test with the methods attackers use today - not yesterday's.
Will you be detected during testing?
That depends on the test purpose.
In a blackbox pentest, our goal is to remain as undetected as possible - just like a real attacker. We develop our own tools and adapt our techniques to bypass antivirus, EDR, and other protection systems.
In a whitebox pentest or upon your request, we can also deliberately use "louder" approaches to test your detection systems.
Many standard pentesters are detected immediately because they only use known tools. This makes the test unrealistic. We do things differently.
What happens after the pentest?
After the final report and results discussion, you have several options:
- Independent implementation: Your IT fixes the vulnerabilities themselves
- Support from us: We assist with implementation (optional)
- Retest: We verify after a few weeks/months whether the issues are fixed
- Regular pentests: Many clients have annual testing
The retest of originally found vulnerabilities is included - you only pay if new tests are added.