Reverse Engineering: Technical Analysis of Software, Firmware and Malware
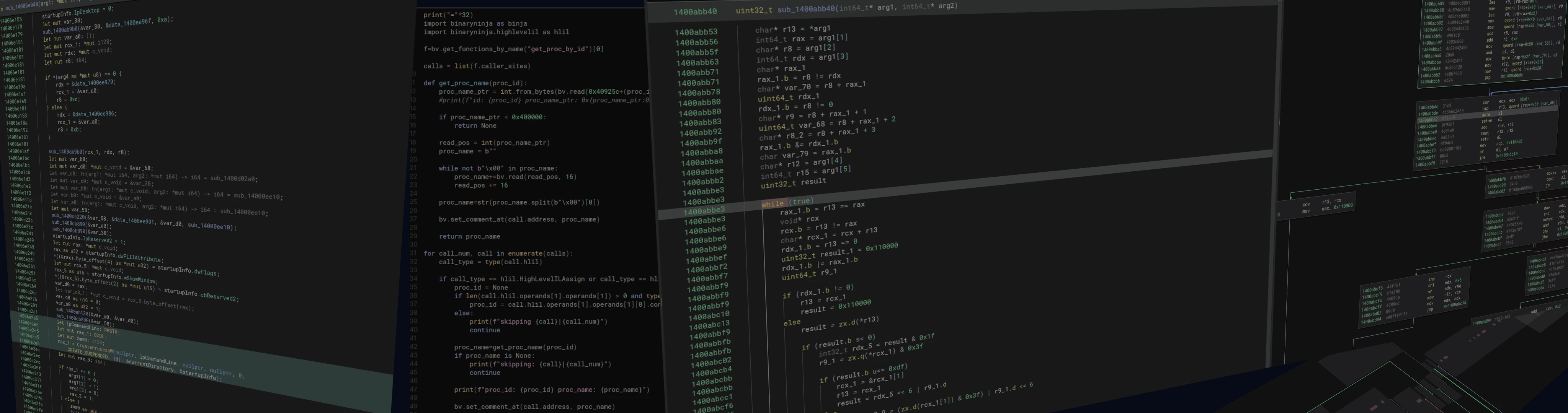
At 0xda7a, we specialize in reverse engineering (RE) services for software, malware, embedded firmware and proprietary applications - regardless of platform, operating system or hardware. Whether your organization is facing malware threats, needs to understand older or proprietary software, or wants to evaluate the security of third-party applications: we provide precise technical analysis and tailored solutions. Our work offers deep insights into internal logic, uncovers vulnerabilities and provides the technical foundation to maintain, secure and further develop software even without access to the original source code.
What is Software Reverse Engineering?
Forward Engineering
A developer writes the source code of a program, documents its functionality, and compiles it into machine-readable binary code.
Everything is transparent because structure, logic, and behavior are visible in the source code.
Reverse Engineering
Reverse engineering is the opposite situation: you only have the compiled program - pure binary code such as program.exe, without source code or documentation.
The goal is to reconstruct how the software works internally, understand its components, and identify how the logic and data flow are structured.
Reverse engineering (RE) is the process of analyzing software or firmware to understand its structure, functionality and internal logic - regardless of whether source code is available. This is particularly relevant for older applications, proprietary systems, poorly documented firmware or malware.
Reverse engineering includes, among other things:
- static analysis
- dynamic debugging
- control-flow reconstruction
- protocol and interface analysis
- binary analysis
These methods make it possible to identify vulnerabilities, extend functionality, understand interfaces and keep systems usable in the long term.
Our Reverse Engineering Services
We offer a comprehensive range of reverse engineering (RE) services to help organizations understand, maintain, modify or secure software without source code.
Extracting Information from Software
Many organizations rely on proprietary or legacy software for critical processes, but without access to the original source code it becomes difficult to fix issues, modify functionality or develop the software securely. We fully analyze applications, document internal behavior and provide the foundation for maintenance, hardening and modernization.
Modifying Software (Patching)
When only compiled binaries exist, we can extend functions, change behavior or adapt existing functional blocks. This includes adding new features, removing problematic modules or modifying interfaces and workflows by adjusting the binary code.
Security Audits & Vulnerability Identification
Reverse engineering is a core component of comprehensive security assessments. We identify vulnerabilities, hidden features, backdoors, misconfigurations and potential exploit vectors before attackers can use them.
Firmware & Embedded System Analysis
Embedded systems often rely on proprietary or poorly documented firmware. We analyze firmware for all common and historical platforms such as STM32, ESP32, 8051, PIC, Renesas and many others. We identify vulnerabilities, behaviors, hardcoded data, proprietary protocols and optimization opportunities - and modify the firmware directly if required.
Malware Analysis & Incident Response
We dissect and analyze malware samples completely - including behavior, attack vectors, persistence mechanisms, encryption routines and internal logic. In incidents, we identify infection paths, damage, Indicators of Compromise (IOC), Indicators of Attack (IOA) and recovery options and provide actionable measures to contain and harden affected systems.
Security Audits for Third-Party Software
Organizations often use external applications without knowing how they work internally or what risks they pose. We reverse engineer third-party software, identify vulnerabilities, misconfigurations or intentionally hidden functions and assess the risks for your environment.
Interoperability & Interface Reconstruction
We reconstruct proprietary protocols, file formats, Application Programming Interfaces (API) or device interfaces to ensure compatibility with modern systems - ideal for legacy environments or discontinued hardware.
Use Cases for Reverse Engineering
Our reverse engineering services solve real technical challenges, such as:
Reviving and modernizing legacy software - Without source code, many older systems can hardly be maintained or extended. We document internal logic and enable updates, extensions or migrations.
Modifying unsupported applications - When vendors discontinue support, we help extend functionality or fix issues - even in historical software or firmware.
Security audits for third-party software - We uncover vulnerabilities, misconfigurations and hidden features to minimize risks.
Malware Incident Response (IR) - We analyze malicious code in technical detail, extract Indicators of Compromise (IOC), assess damage and assist with recovery and hardening.
Case Studies
Extending the Functionality of an Industrial Device
A company needed new features for specialized hardware from a manufacturer who had stopped providing updates. Through firmware reverse engineering, we implemented the required functionality and made the existing hardware fully usable again.
Vulnerability Analysis in a Financial Application
We identified multiple critical vulnerabilities in a sensitive financial application. Working closely with the development team, we resolved the issues and significantly improved the application's security posture.
Malware Analysis for a Healthcare Provider
A ransomware variant threatened the operations of a medical organization. We analyzed the malicious code, identified the encryption techniques and helped develop an effective recovery strategy.
Reverse Engineering of a Legacy Control System
An industrial control system ran on outdated software without source code. Through reverse engineering, we reconstructed its functionality and enabled a migration to modern hardware - without interrupting production.
Process
0Confidentiality
All data is treated confidentially and deleted after completion. A Non-Disclosure Agreement (NDA) can be provided.
1Sending Data and Defining the Goal
You send us software, firmware or malware samples and describe your objectives.
2Free Initial Assessment (approx. 30 minutes)
We evaluate the samples free of charge and provide feasibility, effort estimation and cost projections.
3Your Decision
You decide whether to proceed.
4Full Analysis
We perform a thorough analysis and provide a structured report with technical insights, risks, recommendations and/or a modified version of the sample.
5Time Adjustments
Additional effort is only billed with prior approval. If the task requires less time, costs are reduced accordingly.
Need Software Analyzed? Let's Talk
Pricing
| Duration | Price | Details |
|---|---|---|
| Initial assessment (approx. 30 min) | Free | Feasibility check |
| First hour | 250 EUR | Base fee |
| Additional hours | 200 EUR per hour | Regular analysis time |
| Additional effort | 150 EUR per hour | Only after approval |
All prices exclude VAT.
Frequently Asked Questions
Is reverse engineering legal?
Yes, under certain conditions.
In Germany and the EU, Sections 69a and 69d UrhG explicitly permit:
- Studying software to understand its functionality
- Decompiling for interoperability purposes
- Security research and analysis
In the United States, reverse engineering is also permitted for interoperability, security research, and under Fair Use provisions.
We advise on legality for your specific case if needed.
What data do I need to provide?
We need the binary files, firmware, or malware samples and a description of your goal.
Helpful additional information:
- Known behavior or features
- Version numbers or software origin
- System environment (OS, hardware platform)
The less information available, the more interesting the analysis - we're prepared for that.
Do you work with protected software?
Yes - that's our specialty. Whether packers, obfuscation, anti-debugging, virtualization, or custom loaders: we analyze heavily protected software daily and can often bypass or remove protection mechanisms.
Stronger protection means more effort - that's why we offer a free initial assessment.
Can you modify software without source code?
Yes. We can patch binaries to add features, change behavior, or remove functionality.
Examples:
- Enabling disabled features
- Adding new protocols or interfaces
- Adjusting hardware dependencies
- Removing faulty modules
What if the analysis isn't feasible?
Then you pay nothing. The initial assessment is free, and if we determine the project isn't feasible, we tell you upfront.
No hidden fees.
How do you ensure confidentiality?
All data is used only for the agreed purpose and permanently deleted after completion.
We sign an NDA upon request.
Can reverse engineering damage my software?
No - we never modify your original files. All analysis happens on isolated copies in a secure environment.
What deliverables do we receive?
Depending on the project:
- Clear summary of findings
- Technical details on behavior and internals
- Identified vulnerabilities and risks
- IOC/IOA for incident response
- Patches, tools, or implementations as requested
- Management or auditor-friendly versions available
Do you analyze industrial systems?
Yes. From industrial controllers to proprietary protocols to legacy microcontroller families like 8051, STM32, PIC, or Renesas - we analyze systems regardless of age or documentation quality.
Can you create working implementations?
Yes. After analyzing protocols or formats, we can create functional proof-of-concepts or implementations in Rust, C, or Python.
Results include parsers, protocol implementations, analysis tools, and integration libraries.
What platforms do you support?
We work platform-independently:
- Windows, Linux, macOS binaries
- Firmware from all major microcontroller families
- ELF, PE, Mach-O and proprietary formats
- Virtual machines and containers
Do you offer long-term support?
Yes. For proprietary or undocumented software, we offer:
- Regular security assessments
- Migration and modernization support
- Ongoing patches and modifications
- Vulnerability monitoring